Quantum algorithms and blockchain's vulnerabilities against them
An In-Depth Analysis of Quantum Computing Fundamentals, Key Quantum Algorithms like Shor’s and Grover’s, and Their Potential to Compromise Blockchain
Introduction
Blockchain technology has long been praised for its transparency and immutability. With complex cryptographic algorithms, it has become the backbone of cryptocurrencies, decentralized applications, and digital trust systems. Until now, blockchain has been considered practically unbreakable.
But a new contender is emerging on the horizon, which is none other than “Quantum Computing”. Still in its early stages, quantum computing has the potential to revolutionize how we solve complex problems. It uses the laws of quantum mechanics to process information in ways that classical computers simply can't do. While this opens exciting doors in fields like medicine, artificial intelligence, and logistics, it poses a serious question:
What if quantum computers become powerful enough to break the cryptographic foundations that keep blockchain secure?
So well through this article, we will explore these concepts in a deeper and more engaging way. By the end of this article, we will have a clear understanding of quantum computing and the serious threat it poses to blockchain technology and yes it will compel you to think critically about the future of our digital world.
What is Quantum Computing?
Quantum computing is the type of computation that uses laws of quantum mechanics to process data faster than our classical computers.

It is totally different from our classical computer which uses transistors to represent binary values (0 and 1), whereas in quantum computers, we use quantum properties like the spin of electrons to represent qubits.
Now what are qubits in Quantum Computing?
Qubits, short for quantum bits, are the fundamental units of information in quantum computing, just like bits are in classical computing. But unlike classical bits, which can only exist in one of two states (0 or 1), a qubit can exist in a state of 0, 1, or both at the same time, thanks to a quantum property called superposition.

But why only Qubits?
The power of quantum computing comes from entangling multiple qubits and putting them in superposition, allowing a quantum computer to process an enormous number of possibilities simultaneously, which is impossible for classical computers. For example, while 10 classical bits can store 1 of 1,024 states at a time, 10 qubits can represent all 1,024 states at once. How?
A single qubit can be in a state that is a combination of 0 and 1 at the same time. When you have multiple qubits, each one in superposition, their combinations multiply exponentially.
So:
1 qubit → 2 states in superposition
2 qubits → 4 states in superposition
...
10 qubits → 2¹⁰ = 1,024 states, all at the same time!
This is what gives quantum computers their incredible potential.
Key principles:
Superposition allows qubits to be in multiple states at once (both 0 and 1 simultaneously), which means quantum computers can explore many possible solutions at the same time.
Entanglement is a phenomenon where qubits become interconnected such that the state of one instantly influences the state of another, no matter the distance between them. This enables highly coordinated and efficient computation.
Quantum interference allows quantum algorithms to amplify the correct paths or solutions and cancel out the wrong ones, leading to faster and more accurate results.
Together, these principles give quantum computers the ability to perform certain calculations exponentially faster than classical systems.
How Quantum Computer Works?
Quantum computers operate using quantum gates, which manipulate qubits by changing their probabilities and phases, unlike classical logic gates that just flip bits. These gates are applied through carefully controlled quantum circuits, executed using microwave pulses, lasers, or magnetic fields depending on the type of quantum hardware.
A quantum algorithm typically starts with initializing qubits, putting them in superposition, entangling them, and applying a sequence of quantum gates. At the end, the system is measured, and the quantum state collapses to give the final answer.
Because quantum systems are extremely sensitive to noise and external interference, quantum computing also requires error correction techniques and often operates at ultra-low temperatures to maintain stability.
Origin of Quantum Computing
You might be surprised to learn that the idea of quantum computing didn’t originate from engineers or programmers, but from physicists who were trying to understand the strange behavior of particles at the quantum level. In 1981, physicist Richard Feynman questioned why classical computers struggled to simulate quantum systems. This led to the idea that a computer based on quantum mechanics could solve problems far beyond the reach of traditional machines.

Later, David Deutsch proposed the model of a universal quantum computer, and key breakthroughs like Shor’s algorithm (1994) and Grover’s algorithm (1996) showed its real-world potential, especially in breaking classical cryptography.
Today, this once-theoretical concept is rapidly advancing, backed by tech giants, governments, and researchers worldwide.
Quantum vs Classical Computing
| Feature | Classical Computers | Quantum Computers |
| Basic unit | Bits (0 or 1) | Qubits (0, 1, or both at once due to superposition) |
| Processing type | Deterministic | Probabilistic |
| Power | Linear | Exponential (For n Qubits, 2n states) |
| Limitation | Slower | Error prone and still in early stage |
Quantum Algorithms
Quantum algorithms are specially designed instructions that take advantage of quantum mechanics principles like superposition and entanglement to solve problems much faster than classical algorithms.
Two of the most famous quantum algorithms are:
- Shor’s Algorithm:
Since many encryption systems, including those securing blockchain, rely on the difficulty of factoring large numbers (like RSA), Shor’s algorithm can simplify this task exponentially.
Shor’s Algorithm, developed by mathematician Peter Shor in 1994, is a quantum algorithm designed to efficiently factor large numbers, something classical computers struggle to do quickly.
How Shor’s Algorithm Works:
Step 1: Choose a number to factor
Let’s say: 15
N = 15 (for simplicity)
Step 2: Pick a random number ‘a’ that is less than N
Let’s pick: a = 2
Step 3: Find the period (r) of the function:
f(x) = a^x mod N
So in our case:
f(x) = 2^x mod 15
On computing:
2¹ mod 15 = 2
2² mod 15 = 4
2³ mod 15 = 8
2⁴ mod 15 = 16 mod 15 = 1
Here, the result repeats every 4 steps, so the period r = 4
Step 4: Use r to find the factors of N
If r is even, compute:
gcd(a^(r/2) - 1, N) and gcd(a^(r/2) + 1, N)
So in our case:
a^(r/2) = 2^(4/2) = 2² = 4
On computing:
gcd(4 – 1, 15) = gcd(3, 15) = 3
gcd(4 + 1, 15) = gcd(5, 15) = 5
So, we find the factors of 15: 3 and 5
Factoring small numbers like 15 is easy even for classical computers. But when N becomes a 2048-bit number, classical factoring can take billions of years, while Shor’s algorithm could factor it in hours or days on a large enough quantum computer.
2. Grover’s Algorithm:
While Shor’s Algorithm threatens public-key cryptosystems like RSA, Grover’s Algorithm poses a different kind of risk, it can speed up brute-force attacks on symmetric encryption and hash functions, which are widely used in blockchain security, such as in digital signatures, transaction hashing, and consensus mechanisms.
Grover’s Algorithm, developed by Lov Grover in 1996, is a quantum search algorithm that can find a specific item in an unsorted database √N times faster than a classical algorithm.
How Grover’s Algorithm Works:
Let’s imagine a classical scenario:
You have a locked box that opens with a 64-bit key. To guess the correct key, a classical computer would need to try up to:
2⁶⁴ ≈ 1.8 × 10¹⁹ combinations
On average, it would take half that time to find the correct one, still a huge number!
But a quantum computer using Grover’s Algorithm can do this in roughly:
√2⁶⁴ ≈ 2³² ≈ 4.3 × 10⁹ steps
That’s an exponential speedup going from billions of years to something theoretically achievable in days or hours, depending on the key size and quantum power.
Steps of Grover’s Algorithm:
1. Prepare all possible states (superposition):
The quantum system initializes in a superposition of all possible keys.
2. Oracle Function (black box):
It flips the phase of the correct answer (the marked item) without revealing which one it is.
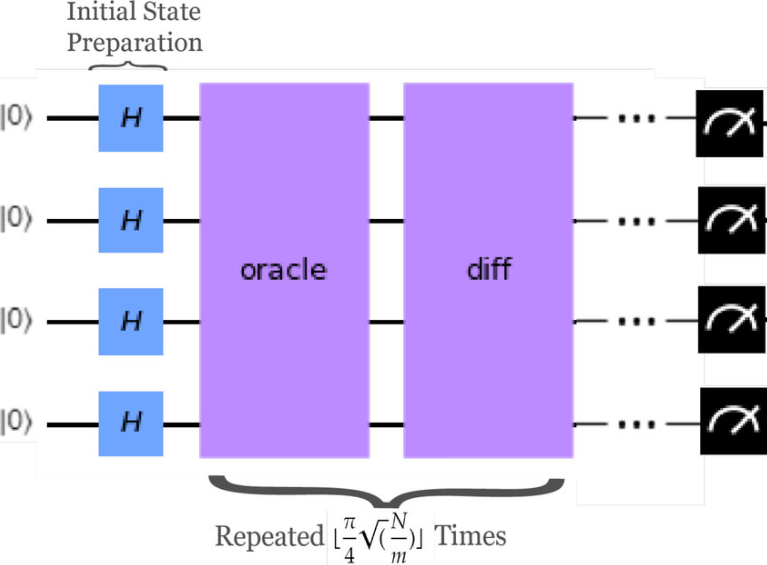
3. Amplify the right answer (Grover Diffusion):
It increases the probability of measuring the correct answer using interference.
4. Repeat √N times:
By repeating the oracle and diffusion operations about √N times, the probability of measuring the correct answer becomes very high.
Grover’s Algorithm may not destroy blockchain security overnight, but it erodes the strength of cryptographic systems much faster than classical brute-force methods. It forces us to re-evaluate key sizes, hash functions, and proof systems to prepare for a post-quantum world.
Threats to Blockchain
Until now, we admired quantum computing for its incredible potential, it felt like a revolutionary breakthrough. But then came a twist. What we considered a technological marvel turned out to be a double-edged sword. We were mistaken. As much as quantum computers help us solve complex problems faster than ever, they also pose a serious threat to the very foundation of our digital security.
We know that blockchain technology relies heavily on cryptographic techniques such as public-key cryptography and hash functions to ensure security, privacy, and immutability. However, with the advent of quantum algorithms, these foundational cryptographic methods are at risk.
Breaking Public-Key Cryptography: Algorithms like Shor’s can quickly solve problems (e.g., factoring and discrete logarithms) that classical cryptography depends on, potentially exposing private keys and allowing attackers to forge transactions or steal assets.
RSA Example(Factoring):
RSA uses a public key: N=pq, where p & q are large prime numbers.
The Private key depends on knowing p and q, which classical computers cannot find easily if N is too large.
But, Shor’s Algorithm solves this in polynomial time:
It transforms the factoring problem into a period-finding problem:
Given: f(x) = a^x mod N
Goal: To find the period r such that a^r mod N =1
Once r is known, we will compute gcd:
gcd(a^r/2 - 1, N) and gcd(a^r/2 + 1, N)
This gives the prime factors p and q and breaks RSA.
Weakening Hash Functions: Grover’s algorithm can accelerate the process of finding hash collisions, which can undermine the integrity of blockchain data and consensus mechanisms.
Grover’s Algorithm gives a quadratic speedup:
It can find a pre-image in roughly 2^(n/2) operations.
For SHA-256: reduced to 2^128 operations.
For finding collisions, it’s even more efficient.
In a simple way:
Hash output: 256 bits
Classical brute-force time: 2^²56
Grover’s speedup: O(√N)= 2^128
Compromising Digital Signatures: Digital signatures authenticate blockchain transactions, quantum attacks could forge signatures, breaking trust in the system.
Most blockchains use ECDSA (Elliptic Curve Digital Signature Algorithm).
ECDSA security relies on the Elliptic Curve Discrete Logarithm Problem (ECDLP):
Q=k . G
Where G is a generator point on an elliptic curve, and k is the private key.
Given Q, it's hard to find k classically.
But Shor’s Algorithm can solve ECDLP in polynomial time, just like factoring.
If quantum computers become powerful and stable enough, current blockchain protocols could become vulnerable, threatening decentralized security.
Post-Quantum Security
Recognizing the quantum threat, researchers are developing post-quantum cryptography.
Key approaches include:
Lattice-Based Cryptography: Uses complex mathematical structures that quantum computers find hard to break.
Hash-Based Signatures: Secure digital signatures based on hash functions, resistant to quantum attacks.
Code-Based Cryptography: Utilizes error-correcting codes to secure information.
Blockchain developers are also exploring quantum-resistant blockchain protocols that integrate these new algorithms to future-proof security.
Conclusion
Quantum computing promises revolutionary advances in computation, but it also poses serious threats to existing security systems like blockchain. Understanding quantum principles, algorithms, and their implications is essential to prepare for a future where quantum attacks are possible.
But also by advancing post-quantum cryptography and adapting blockchain protocols, we can safeguard decentralized technologies and ensure the security and trust that blockchain promises continues well into the quantum era.